Sudarshan Started the session of 4th day by introducing new technical terms and discussed about the previous worksheet he had given in day 3. Apparently, the worksheet is based on Web Application security as well as ZAP source code.
In this session we introduced the main functions in ZAP as well as the package located in and gave a little talk on ZAP API how to access it. ” Curl ” , a tool which helps to transfer the data to or from a server and “HttpOnlyFlag”, which is used to prevent the malicious code from sending the data from our website to attackers website.
Later we introduced about ” Saros “plugin , which is a Collaborating tool for Eclipse IDE, It’s actually essential for a team of members who work on a single project so that they can be on sync with the modifications done during the project real-time working process.
Saros is very useful application which includes features like chat option with the team members, current view of other users who are working on the project.
Sumanth later, started sharing some knowledge about the User interface modules of ZAP tool. He explained about, the way the packages are split in the ZAP source, instead of researching for those packages from all the files. It’s a heck long procedure by the way!
Later myself and sudarshan explained about Swing Explorer which is an open source tool used on any Swing based applications to explore swing elements like Windows, Frames, Buttons and a few other elements visually. Actually, we can browse all the hierarchy of the components. We also taught them about how to add new tabs in different positions of ZAP User interface like ” Left “, ” Right ” , ” Footer “, etc..
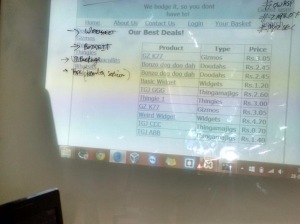
“The Bodgeit Store ” which is a vulnerable application actually developed for newbies to work on penetration testing.
Bodgeit Store is made of few vulnerabilities like :
1. Cross Site Scripting
2. SQL injection
3. Unprotected content ( hidden )
4. Cross Site Request Forgery
5. Debug Code
6. Insecure Object References
7. Application Logic vulnerabilities